Note: As a professional courtesy to those at Adobe who are doing their absolute best to mitigate this breach, I have partially redacted all full hashes and email addresses from this blogpost, besides those found in the image published by arstechnica.com.
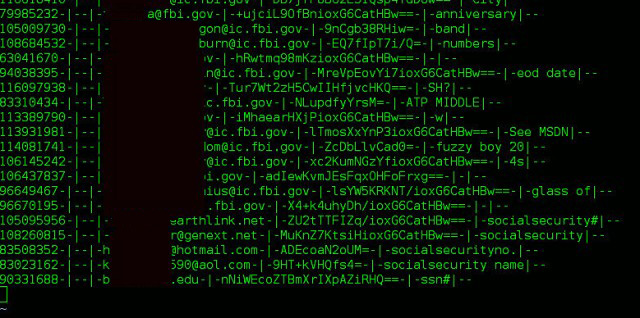
We all know about the recent 153 Million account dump from Adobe. As arstechnica showed, the format looks something like this:
Image source: http://arstechnica.com/security/2013/11/how-an-epic-blunder-by-adobe-could-strengthen-hand-of-password-crackers/
As you can see, there's some sort of ID number, the email address, the encrypted password (which from the arstechnica article we now know is 3des) and the password hint.
Password hints are great and all, but they can be unreliable, unclear, or flat out wrong.
HOWEVER, when you have thousands of people using the same password (same encrypted string) looking at all of those password hints together can make the cleartext password painfully obvious.
For example. Let's get the most common encrypted password strings from the dump (with numbers on the left showing how many times they were used):
1911867 EQ7fIp*****=
446144 j9p+********************==
345833 L8qbAD**********CatHBw==
211659 BB4e6X+b*************w==
201569 j9p*****2ws=
124248 dQ*****PYvQ=
113880 7*****Veq8I=
83409 PMDTbP**********FUvYGA==
Now let's take that first, most common password string, and go get all the users' hints who used that same password. Let's also uniq those and sort them by how popular that actual hint is:
One can reasonable guess what password corrisponds with EQ7fIp******=
Now let's see what else we can do with this. Let's use this same method to see if we can target an individual account in the Adobe dump. Funny enough, there's an entry for an account edwardsnowden@******mail.com.
6**58***-|--|-edwardsnowden@******mail.com-|-B***************CatHBw==-|-|--
Now let's see if any other people in the dump have the exact same password hash as this account, and if so then how many.
[jdustin@localhost passwords]$ grep B***************CatHBw== cred | wc -l
Okay, let's grab those 207 the lines containing all accounts who used that same password, cut out just their password hints, and then sort them by how often that hint is in the list:
[jdustin@localhost passwords]$ grep B***************CatHBw== cred | cut -d"|" -f5 | sort | uniq -c | sort -nr | head -n50
So, Metal? 74W on the table of elements? The usual Tung?
"tungsten" perhaps? Your guess is as good as mine. :)




This comment has been removed by the author.
ReplyDeleteWhere did you download the file?
ReplyDeleteI was discussing this last week in the context of password reuse. I did a bit of "research" and found that of the brute forced pws from the dump many are used across major sites. Password reuse is a real problem and people don't appreciate the implications.
ReplyDeleteHey ,
ReplyDeleteI will try it and discuss it in our Community of graphic designers .password reuse is a biggest problem but the people..............
I enjoyed the tips you are providing on your website. Adobe support can make one’s help technical service. Thanks for the information……..
ReplyDeleteAdobe Support please visit the link.
Thankyou
Lacy Brown
I am very happy to see your blog, good article and interesting,
ReplyDelete*reach your marketing lists or Sales Leads*
Email Appending list is continuously updated with most accurate, quality and verified contacts.
Ehealthcarelists can provide Adobe Users
Email complete marketing information such as
· First Name, Last Name
· Business Name
· Practice Specialty, Specialty Code
· Email, Postal Address and Zip Code
· SIC /NAICS Code and NPI Numbers.
· Phone Number and Fax Number
· License Number
· Web address
Thanks for the information and Greetings
I am glad to see this post which I was finding. It is incredible post. The personal statement length are available here for those who are thinking about to draw the graph.
ReplyDeleteCollections from the design labels such as pas cher trx and other beauty are released after every six months.
ReplyDeleteWith every new launch, a new penny skateboards cheap online technology is developed.
This had led to making TRX For Sale remain competitive in the International market.
The entire pas cher trx packaging process is paid into detail to enhance the collections quality and appearance.
Now everyone can own high-end designer trx france.
TRX Suspension Training Sale being one of the largest and most prominent fashion company in the world, it has an obligation of beating the standards set by others.
The fashion world, with a higher concentration on Discount TRX Sale, needs to provide the best packaging services that the modern world has ever seen.
TRX Suspension Training On Sale plays a major role in creating a brand name that fashion lovers want to identify with.
Support for adobe +1877-339-8403. Our highly knowledgeable Adobe technical support online staff is readily available at all times for our well- regarded clients to help out with their Adobe issues at the earliest possible time.
ReplyDeleteTollFree +1(855)837-9965! Repair All PC, LLC in Cleveland Ohio. Our Microsoft certified professionals & System Engineers which provide Best Tools and Expert Solutions to all you issues on repairallpc.net
ReplyDeletesuch agreat blog,nicely explained thanks to shared this blog about email list Email Appending | B2b Email Appending
ReplyDeleteGreat blog! I really love how it is easy on my eyes and the information are well written. I am wondering how I might be notified whenever a new post has been made. I have subscribed to your feed which really should do the trick! Have a nice day! We provide you online help and support.Call us at Our Adobe Customer Care Number UK0800-098-8579.
ReplyDeleteReally i appreciate the effort you made to share the knowledge. The topic here i found was really effective to the topic which i was researching for a long time. Adobe Contact Number UK
ReplyDeleteYou can get touch with us by dialing our Adobe Helpline Number UK@0800-098-8312 for any technical problem. We provide you solutions for resolving problems shortly or related issues.
ReplyDeletegreat article about email appending appreciate the way presents of blogs and words.nice job!
ReplyDeleteEmail Appending Services
Great blog! I really love how it is easy on my eyes and the information are well written. I am wondering how I might be notified whenever a new post has been made. I have subscribed to your feed which really should do the trick! Have a nice day! We provide you online help and support.Call us at Our Adobe customer care number 0800-098-8579.
ReplyDeleteThis was really an amazing blog to read. Thanks for sharing it with us and keep on sharing information like this. For any type of other information regarding Adobe get connected with us at Adobe Support Number UK.
ReplyDeleteThis research is practically done by you and gives good ideas. visit here some useful content here
ReplyDeleteAdobe contact help Number US +1-844-442-0111
Adobe support helpline Number USA
This comment has been removed by the author.
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteBest Blog for Information about of "Hotmail Account" & Thanks for sharing with me. This blog is very helpful. If Any Hotmail users have got some technical error in our Mail Account so don't worry quick consult at toll free @08000988343 Hotmail contact number UK and get resolution for all these error.
ReplyDeleteThanks for sharing nice information with us. I like your post and all you share with us is up to date and quite informative.
ReplyDeleteGet help for Dell printer technical support.
Dell Printer Contact Number UK
Dell Printer Support Number UK
Thank you very much! Your blog is always full of great idea. They are really helpful
ReplyDeleteAdobe Customer care Number
Hotmail Helpline Number UK
ReplyDeleteIf you facing this problem while using the account and the best way to resolve this problem is to contact the technicians at 08000903883 toll-free number.
Hotmail Customer care Number UK
This comment has been removed by the author.
ReplyDeleteHello, I really like your post and i am glad that you shared this useful info with us.
ReplyDeleteContact Hotmail Helpline Number For UK and tech expert suggestion.
Best Blog for Information about of "Hotmail Account" & Thanks for sharing with me. This blog is very helpful. If Any Hotmail users have got some technical error in our Mail Account so don't worry quick consult at toll free @08081013524 Hotmail phone number UK and get resolution for all these error.
ReplyDeleteVery Nice post. I liked the way you explained it clearly like I saw in Automation Associates LLC. Thanks for sharing.
ReplyDeleteVery Nice Post. I congratulate with your blog. Thanks for sharing. You can also publish this excellent post on other platforms such as, Wordpress, Blogspot followed by Livejournal, Medium and Tumblr
ReplyDeleteExcellent and amazing post. Worth the time. You can also share these post in different social medias to get a higher ground like Facebook, the famous Twitter and in the LinkedIn profiles followed by Google Plus and the Infographic Site Pinterest.
ReplyDeleteBeautiful post I've come across today. Informative. Thanks for sharing this most excellent information. You can share this information on other platforms such as, Wordpress the most useful Blogspot site followed by the famous Tumblr and also in Medium lastly in the Live Journal site.
ReplyDeleteGreat post, and I am glad that you shared this useful info with us. This blog is very helpful. You can also share this Information on many other sites for example like Free Samples 411, a clean business site like OS Business Opportunities swiftly followed by Jfissures and Asaimjapan and also the Johny Adams site.
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteHi, Wonderful blog. I really like this. Get in touch with the tech expert any time you require resolution for your Microsoft tech issue by just one call at Microsoft Contact Number UK instantly.
ReplyDeleteThanks for sharing this informative nice article and good work
ReplyDeletenba2k14 crack
tally torrent download
Highly effective hackers have very unique habits that set them apart from other hackers. Therefore, any young professional hacker should adhere to the outlined habits if they want to be specialists and gurus in their profession. I will be recommending this site to our clients who are majorly students accessing our US English Essay Writing Help.
ReplyDeleteThis research is practically done by you and gives good ideas. visit here some useful content here
ReplyDeleteMcAfee Support Number UK 0800-756-3354
Accomplishing your daily works with the help of Adobe Application on your computer, but technical issue are still found in during its use, so you must talk to the technical experts at 0800-090-3220 to get an accurate solution. Adobe Helpline Number UK
ReplyDeleteI have been thinking of how I can start learning about hacking and now I am encouraged. The author of this blog shows good mastery pf hacking techniques. I believe that the beginning hackers have the most reliable information.Custom Help with Med School Personal Statement Writing
ReplyDeleteThankful for such a nice blog ....
ReplyDeleteDell Printer Help Number UK 0808-178-2624
Lexmark Printer Help Number UK
Brother Printer Help Number UK
Canon Printer Help Number UK
Apple homepod
ReplyDeleteApple homepod features
Apple homepod price
apple home entertainment system
the best speakers for iphone
apple homepod sound quality
Cool iphone speakers
wireless home audio system
Nice post i really like it.Call us at 0800-090-3240 Adobe Support Number UK and Adobe Helpline Number UK to get quick and satisfied solution.
ReplyDeleteI have been through your blog and being a technical expert, I found it quite information giving. Here, you forgot to tell about the correct to counter the issue which is to contact the technicians. If one facing any tech problem, then contact us at keyword and for more information follow the link. Hotmail Helpline Number UK
ReplyDeleteIt’s a very helpful post.. Thank you for sharing this post..
ReplyDeleteKodak Printer Support Number UK
Kodak Printer Contact Number UK
ReplyDeleteNice Blog
Norton Helpline Number UK 0800-029-4639
Without a printer, we hardly able to fulfill our daily requirements of office work and Lexmark is that which offers affordable printers. Even so, tech issues are making the users problematic and to encounter with that, you must talk to the technicians at 0800-090-3240. LEXMARK Printer Helpline Number UK
ReplyDeleteNot able to use some tools of Adobe application properly. At this time, you need to contact the technicians at 0800-090-3220 to get the proper resolution of the issue in a short time. Adobe Customer Care Number UK
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteGetting tech complication in using Adobe in your system, so you need the correct assistance from our experts of Adobe Support Number UK & Adobe Contact Number UK to resolve that quickly.
ReplyDeleteSuch a very informative blog. Very interesting to read this blog.I would like to thank you for the efforts.
ReplyDeletethank..! really useful information..
Canon Printer Support Number Uk 0808-178-2624
Canon Printer Helpline Number Uk
Canon Printer Contact Number Uk
Nice blog HP Printer Support Number Uk 0808-178-2624
ReplyDeleteNice Blog! Thanks for sharing nice information with us
ReplyDeleteCall at
Brother Printer Support Number Uk 0808-178-2624
Adobe is a famous operating system across the population of UK. It is an advanced platform to suit your projects to build with. For any technical related errors, you an call our skilled technicians at Adobe Help Number UK & Adobe Helpline Number UK
ReplyDeleteNice Blog.
ReplyDeleteBrother Printer Support Number Uk 0808-178-2624
This comment has been removed by the author.
ReplyDeleteHotmail Helpline provides UK 0800-098-8587
ReplyDeleteToll Free Number to get email account problems resolution in their hotmail / outlook
account.we are best hotmail helpline number in
uk.
Facing Problems in opening Adobe applications, then you must contact the technician at Adobe Help Number UK 0808-238-7544.
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteVery nice post. It’s a very useful and outstanding blog. Call us at McAfee Support Number UK and McAfee Phone Number UK to get quick and satisfy solution.
ReplyDeleteNice Blog, I have been all over your blog and being a technical expert
ReplyDeletequicken helpline number
quicken support number
free daily accounts!
ReplyDeletehttp://freeaccounts4.blogspot.com/
Try phenq coupon at www.increasetestosterone.review
ReplyDeletehp printer helpline number - There are many HP numbers for different problems such as hp support number for casual support, hp customer service number for customer support, hp printer support online. We provide HP printer support online you can call us at helpline number +1-800-787-2406 anytime free of cost.
ReplyDeleteTo take full benefit of all Hotmail features, you need to understand them and configure your account setting. Please dial 0800-029-4639 and make things easier for you. Here you can talk to our Hotmail executives and get proper assistance about Hotmail issues.
ReplyDeleteHotmail Helpline Number UK
NO one can tell you when HP Printer will start to show technical issues, but technical experts are the ones who can tell you how you can settle that within a few minutes. TO know about this, you should talk to them at HP Printer Support Number UK
ReplyDeleteAsus Router Customer Support the problem occurs again, just delete the current network from the list of your saved networks on your device and then reconnect it again.
ReplyDeleteThis post seems to be really nice and helpful. Although, for those who are using HP Printer can connect with us at HP Printer Help Desk Number UK and find the solution for their problems.
ReplyDeleteWe are here to provide the solution to the all the problems related to the Routers. The solutions provided in the link are very good and very easy to implement.
ReplyDeleteCisco Customer Support
nice blog
ReplyDeleteAsus router customer service
thanks for this post.
ReplyDeleteApple Airport Technical Support
nice post thanks for sharing.
ReplyDeleted-link router customer care
if you have any problem related to asus router then they can contact us asus router customer support
ReplyDeletemany people are facing problen in their internet explorer they people can contact us we are here to provide the complete solution about the asusu router support.
ReplyDeleteinternet explorer customer support
ReplyDeleteFed up with the slow working of the Browsers, get your problem solved by clicking on the link given below-
Safari Customer Service
If there is anyone who is not able to understand why some type of technical issues are coming up in Hotmail, then bank on 0800-029-4639. In the market there is no one who can actually transfer good quality of work then don’t panic and refer the experts. Other sources or professionals belonging to other sources do not have the expert knowledge like Hotmail Professionals do possess. Over the years countless times measures are being undertaken for precision being maintained and this is what is raising the bar of efficiency provided by experts of Hotmail.
ReplyDeleteHotmail Help Number UK
Resolving technical issues of HP Printer has been easy for you, as here we are round the clock, available to serve you the accurate solution of the issues in a while at HP Printer Helpline Number UK.
ReplyDeleteHii..
ReplyDeleteNice info.
Adobe Support
Adobe Technical Support Number
Adobe support phone number
Adobe Photoshop Tech Support Phone Number
Adobe illustrator Support
Adobe Dreamweaver Setup Help
Adobe Flash Support Number
http://www.printersupportnumbers.com/
ReplyDeletePrinter Technical Support Number
We have been appreciated by the customers for providing complete resolution in a day by our highly skilled staff and have thousands of satisfied and happy customers by our side.
www.mcafee.com/activate
ReplyDeletewww.mcafee.com/activate
www.mcafee.com/activate
roku.com/link
www.mcafee.com/activate
Nice post, thanks for share info.
ReplyDeleteIf you want to get an instant solution on printers, just call on Canon Printer Toll free Number +1-855-676-2448.
Canon Support Number
Canon Tech Support Number
Canon Printer Support Number
Canon Help Number
Canon Printer Technical Support Number
Canon Support Contact Number
The user does not have to worry about smooth working of Hotmail account. It is simply because of superior form of understanding of the professionals of Hotmail. if there is any technical obstruction like – not able to send or receive emails, difficulty in managing settings, slow working of Hotmail etc. The concerned person needs to just refer to Hotmail Customer Service Number UK.
ReplyDeleteHotmail Support Number UK
Norton has a unique talent for detecting and removing the unwanted threat imposed into your system premises. If you are having any technical problem regarding it, just call the proficient technicians available at Norton Customer Helpline in the UK.
ReplyDeleteNorton Helpline Number UK
Great blog! Thanks for sharing. Are you looking Canon Printer Drivers Support? if you face any issue with your Canon Printer Driver, then contact us at +1-888-600-6920 Canon Printer Drivers Support and get instant solution.
ReplyDeleteWe provide instant solution for solve technical errors call us at +1-855-556-7999 and get help from our experts. If you are facing any technical issue you can contact here anytime.
ReplyDeleteitunes contact us
apple technical helpline
itunes contact support number
itunes contact support
itunes phone number
apples toll free number
apple macbook support number
apple tech support number
apple support customer service
apple helpline toll free number
apple technical support number
mac tech support number
Hii.
ReplyDeleteAdobe Online Support Number
Contact adobe Photoshop Support
adobe illustrator Support Phone Number
Adobe Dreamweaver Phone Number
Adobe Flash Help Number
We cannot underestimate the issues that Hotmail users encounter. It can be anything starting from forgotten password to hacked or compromised account. Technicians of Hotmail Customer Care UK, has thorough knowledge about this service and can help you in dealing with any problem.
ReplyDeleteHotmail Helpline Number UK
thanks for the sharing.such a valuable information.
ReplyDeletenice information for the blog.
nice posting keep it up.
mcafee technical support
mcafee tech support
Not every post is as helpful as this one. We are also offering solution for Hotmail issues, and to connect with us, you just need to make us a call on Hotmail Helpline UK.
ReplyDeleteWelcome to Adobe Support Service. For technical issues, call our toll free customer care number 1-855-676-2448 for help.
ReplyDeleteAdobe Technical Support Number
If you are looking to Adobe support contact number to resolve your problem, please get in touch with our certified technicians to get the best customer support service at highly reasonable prices. Adobe Installation Support Phone Number Adobe Support Number and get instant solution.
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteGood Job... For Microsoft Support Contact US
ReplyDeleteAdobe applications are little tricky one to handle, and when it comes to its complications then it becomes even more difficult for user to resolve them. In such situation, one can get in touch with our software engineers by making a call at n our toll free Adobe Helpline Number UK.
ReplyDeleteA printer user will definitely feel the need of a printer technician at some point of time. If your HP Printer is also showing tantrums to you then feel free to connect with us on HP Printer Technical Helpline Number UK .
ReplyDeleteGet going with AVG antivirus uninterruptedly with the assistance of AVG Support Number +1-855-676-2448.
ReplyDeletehttp://avghelpnumber.website2.me
The user does not have to run here and there for right and precise information about Norton Antivirus. Professionals can be easily contacted through Norton Technical Number UK and then difficulties will be provided with correct solutions. All the experts have thorough knowledge about technical imperfections faced by the user of Norton Antivirus.
ReplyDeleteNorton Support Number UK
This comment has been removed by the author.
ReplyDeleteAt the time to setup your Roku player or Roku TV streaming, You need to connect your device to internet network as you connect your mobile device or your computer.
ReplyDeleteWhy do I see an error message such as “Roku stick not connecting to wifi” or “Roku stick not working on tv”or “Roku stick not working” or “roku stick not connecting”?
Sometime your device not connected properly to your home network or your internet network. These reason to getting this type of error. We are the technical support company provide the online support for your Roku. You can connect with us through dial +1855-559-7111 toll-free or visit our official website: Click Here...
Nice blog, thanks for sharing. If you are looking technical support for your Brother Printer.Then no need to go any where, pick up your phone and dial Brother Printer Helpline Number UK 0800-090-3828 and get instant support.
ReplyDeleteThe user faces any issues with the software can connect to Adobe Support Phone Number 1-855-676-2448 which is available 24*7 to assist the issues.
ReplyDeletehttps://adobe-support-phone-number.webnode.com/
Dial toll-free number +1 (855) 556-7999 & Get Instant Help for All Apple Products. Online Customer Service and Support available for Apple iPhone, MacBook, iCloud, iTunes, iOS, Apple Watch & other Apple products. 24/7 Available Toll-Free.
ReplyDeleteSource available here.
Very nice post. It’s a very useful and outstanding blog. Call us at Adobe Support Number Uk and Adobe Helpline Number Uk to get quick and satisfy solution.
ReplyDeleteThe concerned person does not have to worry about correcting the flaws occurring inside the HP Printer. Professionals should be contacted through HP Printer Helpline Support Number UK and then all major or minor technical glitches will be resolved instantly.
ReplyDeleteNice Informative Blog having nice sharing..
ReplyDeletehotmail sign in account
This helps them to freely browse over internet, without getting trapped by any malicious file or virus program. For any unexpected problem creating hassle in working of this application, contact Norton antivirus help number 0800-041-8339 technicians and ask your queries, so that you can get hold of perfect solutions in shortest meanwhile. http://technicalsupportnumber.co.uk/norton-support/
ReplyDeleteIn case of any flaw with antivirus software, you can dial Avast contact customer care number 0800-041-8301 anytime without giving any thought, as expert techies are available 24x7 to listen all your issues and to provide instant solution. Get hold of best assistance from reliable third party customer service for antivirus issues.
ReplyDeletehttp://technicalsupportnumber.co.uk/avast-support/
Avast Antivirus Help Number
Avast Antivirus Phone Number
Avast Support Number
Avast Tech Support Number
Hotmail Help Number UK
ReplyDeleteHotmail Support Number UK
Hotmail Contact Number UK
Help full post for those people who use computer security. All issue related with your computer Antivirus and security. We provide online solution. For more details
ReplyDeleteKaspersky Live support,
Kaspersky support phone number,
Kaspersky technical support number,
Kaspersky help number,
Kaspersky tech support number,
There may be some employees in your office that are using your business printer for their personal use. If one or two employees are doing so then it won’t cost you must but if a 20-30 employees are doing the same then it might cost you much. Read this blog and learn how to track print job in a better way. To know more about printer, feel free to visit: Canon Printer Technical Helpline UK.
ReplyDeleteNow AOL Customer Support Representatives are available at +1-844-443-3244 Toll Free Number
ReplyDeleteAOL Desktop Gold | AOL Gold Download Link | Download AOL Gold Desktop | AOL Gold Program Download | AOL Gold Desktop Software | Download AOL Gold | AOL Desktop Software Download |How to Download AOL Gold Desktop | Install AOL Gold Desktop | Download AOL Desktop Gold | AOL Gold Download for windows 10
For resolution of technical faults related to AVG connect to AVG technicians by dialing @0800-046-5071 for best and accurate technical assistance.
ReplyDeleteAvg Contact Number UK
Avg Phone Number UK
If your echo won't connect to wifi Or having any problem to setup Alexa to Wifi then Don't Worry we are here to help you just follow the simple steps which is given on our website. We'll help you to connect Alexa to wifi, connect echo to wifi and amazon echo not connecting to wifi and other problems. For instant help call us at our amazon echo dot help number +1-888-409-8111.
ReplyDeletesetup echo.
great blog with useful information..
ReplyDeleteAsus router support
Nothing can stop HP Printer users from printing as they have full support of our experienced technicians. These technicians can help you in eradicating all sorts of printer issues, so that you can print effortlessly. To connect with these printer executives, just one phone call at HP Printer Help Number will do.
ReplyDeleteHey Joshua Dustin,
ReplyDeleteThank you for that great post. It’s my first visit here, we provide best technical support for avast antivirus.
Avast Support Number UK
Avast Contact Number UK
Well, going through your blog certainly helped me to rectify the problems occurring inside the printer. if the user seeks assistance from the source Canon Printer support then answers will be delivered. At this stage, ser will not have difficulty in doing work through Canon Printer. To know more about printer, feel free to visit: Canon Printer helpline Number UK.
ReplyDeleteNice Blog. you share very informative blog with us . Thanks
ReplyDeleteLet us help you with printers, routers, malware , slow laptops, and any other technology issue.Best Buy Systems is your trusted source for technical support in Valencia, California, USA. Our customer service was made to offer US Technical support to the customers on their desk with no interference. For any help you can call us our toll free number +1-888-339-8933 .
If you are using kaspersky antivirus. We provide the best technical support for kaspersky antivirus. If you need any types of help you touch with our kaspersky Contact Number
ReplyDeleteHey..Joshua Dustin..
ReplyDeleteWhat a helpful post.. Thank you for sharing..
Avast Activation Key Number
To make your AVG antivirus work in a proper manner without having any technical problem in future, you need to make sure that your AVG is installed in a proper manner. A corrupt or damaged installation will cause various issues. If you face any issue in installation of this program then you should dial us at AVG Helpline Number UK for guidance.
ReplyDeleteAvast antivirus has three different types of components i.e. security, privacy and performance related. You can manage these components as per your desire. You can enable or disable it, install or uninstall it or customize these components as per your requirements.To know more about printer, feel free to visit: Online Avast Help Number UK.
ReplyDeleteGet Technical Support for Printers more info visit the link HP Printer Support Number Uk
ReplyDeleteYou can try Adobe Customer Support Number 1-855-676-2448 anytime you need help. Trained experts in Adobe software will troubleshoot all kind of technical error in short time period. The service of customer support is 24*7 open for every Adobe users.
ReplyDeleteAdobe Phone Number
Adobe Customer Support
Adobe Customer Service
Most print quality issues are either related to the print head of your Canon Printer or ink cartridge. You need to make sure that there is no blockage in the print head and you should also keep a check on ink cartridge level. In case, the cartridge needs replacement, then dial us at Canon Printer Customer Care Number UK.
ReplyDeleteThe Hotmail issue I was once facing has now resolved. If you are having another such doubt just keep calm and call Hotmail Helpline Support Number UK.
ReplyDeleteVery useful psot you share. Thanks for sharing.
ReplyDeleteIf anybody looking for any type of router support so Best Buy systems is an online service provider for issues related to router. We provide software solutions, technical router support and hardware configurations in one place. For any information call us our TOLL free no. +1-888-339-8933 .
These type of informative blogs always emerge as best solutions for whatever technical error one encounters with thanks a lot my pc is now back to normal. please click on the link below:
ReplyDeleteAvast Help Number UK
Kaspersky Help Number UK
Avg Help Number UK
The user might face some XYZ form of difficulty in the operation of Adobe software. Engineer and another representative of Adobe have been very instrumental in making sure that objective of the software is achieved. Presence of Adobe Helpline Number UKis the ideal form of source for learning about solutions in reference to activation issues arising inside the Adobe Software.
ReplyDelete
ReplyDeleteAOL Mail - Aol Sign in, Sign up, Login etc at AOL com Mail. AOL Email Sign in at Mail.aol.com & Also do AOL Password Reset. My AOL Account at aol.com, login.aol.com, i.aol.com or aol.co.uk
AOL Mail
Webroot SecureAnywhere Antivirus Shield not working – Webroot SecureAnywhere Antivirus includes a number of shields, which works in the background and protects your system. These shields persistently monitor your system and protect your system from the viruses or malware. Webroot SecureAnywhere includes Real-time Shield, Rootkit Shield,
Webroot SecureAnywhere
You can get Norton product from an online store or retail stores. In both cases, you will get Norton product key, using this key you can activate and use Norton product.
norton product key
Talking about different types of problems occurring inside the Hotmail platforms means that experts are supposed to take a peek in the problem. Well, this is why calling professionals through Hotmail Helpline Number UK do guarantee of the speedy and quality form of resolution. Had other sources been referred then corrective actions will always be doubted by the users.
ReplyDeleteCanon printer Support number uk
ReplyDeleteHow to fix AOL mail error code 521? AOL Mail is the most popular free web-based email service provider, which provides many types of services, so users can complete various types of tasks, whether they are professional or personal. While using AOL, users may have to face some errors in it. Fix AOL Mail Error Code 521 One of the most common error
ReplyDeleteGreat! You are providing very useful and amazing knowledge regrading blog..
ReplyDeleteAvast Toll Free Number UK
Avast Contact Number UK
Nice blog. Thanks for sharing this valuable information with us. We offer 24*7 tech support services for router configuration process. If you are looking for the exact services then you can call us for assistance. Our technical expert will provide you top quality services as per your desire.
ReplyDeleteVery interesting , good job and thanks for sharing such a good blog..
ReplyDeleteAvast Refund Number UK
Avast Help Desk Number UK
Hotmail users tend to face multiple issues in sending or receiving mails. If you want to clear off such issues, take the advantage and call at Hotmail Helpline Number UK 0800-029-4639 for instant resolution. This technical service is appreciable attempt for Hotmail issues.
ReplyDeleteYou will surely need technical help when your system is projected to technical errors after installing AVG security. If you are looking for the technical assistance for AVG related errors, then you are recommended to call at AVG Customer Care Number UK for instant help. The technicians are responsible and put every effort for helping you.
ReplyDeleteThe official blog from kaspersky help number provides information with regard to protection of systems and devices from all dangerous malware spyware Trojan and other infections.
ReplyDeleteKaspersky Contact UK - 0800-046-5071 - Blog
Kaspersky Support UK - 0800-046-5071 - Blog
There is no way a user should get blinded when other sources advertise their version of security tool. Having said this, the user needs to understand that way of explaining the working of Avast Antivirus by the concerned professionals is of rich quality. The user does not have to look further than Avast Technical Helpline Number. As it will make be enough for quenching the thirst of query seekers.
ReplyDeleteAdobe has various multimedia products such as Adobe Photoshop, Reader or Acrobat, Flash, Illustrator, Dreamweaver and many more. All these products have proved to be really helpful but they are definitely prone to technical issues and these technical issues can be resolved at Adobe Customer Support Number via software experts.
ReplyDeleteAdobe Support Number
Hey,very useful blog buddy. Thanks for sharing this kind of useful information with us. Call us at any time to avail professional technical support services. We provide 24*7 tech support services for printers, routers, PC optimization and website malware removal. So if you want to avail any of our services then contact us at our toll free number +1-888-339-8933 .
ReplyDeleteNothing will ever bother you if you just take support of our technical team to address your issues related to Avast antivirus. One call at Avast Helpline Number UK will change the way you look at its technical issues. You can ask anything from these technicians associated with Avast.
ReplyDeletePrinting and scanning issues in HP Printer? Dial HP printer support phone number or get free tool HP Print and Scan Doctor to diagnose and resolve problems.
ReplyDeleteNice Post!!
ReplyDeleteHello Admin this is the good information for us please go through -We also provide tech support services for Antivirus users. You can dial our toll-free Antivirus Support Number +1-800-241-5303
ESET Nod32 Antivirus Technical Support Number
Microsoft Security Essentials Help Number
Trend Micro Support Phone Number
AVG Customer Support Number
McAfee Toll-Free Number
Kaspersky Help and Support
Avast Antivirus Customer Services Number
Norton Internet Security
Thank you Best Buy Systems for assisting me for technical support. great work done.
ReplyDeleteYou have done a great job by posting this blog here. AVG people can reach us on AVG Customer Support Number UK anytime if they are having any query about AVG product. Our tech team will help you dealing with every issue.
ReplyDeleteIf you are also facing any such issue in dealing with any Adobe application, then you can contact the Adobe support number 1-800-301-3935 for instant technical support. We offered dedicated 24 x 7 technical support all across the USA for dealing with such issues instantly.
ReplyDeleteAdobe support Number
Adobe customer support
Hotmail sync related issues can arrive at any point of time. The thing is what one should do to rectify such errors. The technical team at Hotmail Customer Care Number UK is the right choice for fixing whatever error you have came across. Call them at 0800-029-4639 and ask anything you want to.
ReplyDeleteThere is no point wasting precious time in referring non-functioning form of sources for correcting flaws in Hotmail. For any difficulty like – Hotmail is not loaded in any browser, not able to configure the settings the account has been hacked etc. So, the best way out are Hotmail Contact Number UK and the answers will be received by the Hotmail users. Apart from Hotmail professionals no other is able to proceed with the corrections.
ReplyDeleteMany thanks for sharing this information. We know how good it feels to help people get rid of their issues as we to offer quick support for McAfee on our 24x7 McAfee Customer Care Number UK.
ReplyDeleteMcAfee Helpline Number UK
If Kaspersky security is making your system work slowly, you should connect the technical executive by Calling at Kaspersky Support Number UK for full support. The experts will tackle the situation with their expertise skills with the shortest period possible.
ReplyDeleteThanks for sharing this marvelous post. I m very pleased to read this article.
ReplyDeleteWe provide free service of some site like if you want to download office setup visit on this site:office.com/setup,
office 2016 setup,office 365 setup,For norton antivirus visit here:norton.com/setup, norton.com/nu16 For more sites and free tech blog visit on site below
IT support
During conducting a work if the user finds difficulty in resolving the scan related problems, difficulty in installing the antivirus, the correct form of internet security steps is not followed etc. In these sorts of situations, the user just needs to refer professionals through Norton Technical Helpline Number.
ReplyDeleteAdobe is regarded as the best application for completing different tasks. If you want to deal with some unknown errors, connect the technical team at Adobe Help Number UK for the best fixation method.
ReplyDeleteNeed of printer may come at any time at home or at office and for all such there is only one printer brand that is renowned for its service and that is Canon. The printers of Canon have done tremendously good in terms of printing quality and with that the printer users are fed up with the technical errors arising in the printer. Resolving the printer tech issues is a tough task indeed and in order to get the issue corrected get connected with the experts at Canon Printer Help Number UK. Tech issues can be associated with any part of your printer and all such issues can be corrected easily.
ReplyDeleteMcAfee Installation is such an easy or simple process as you have to make sure that above-mentioned prerequisites should be fulfilled before getting started with the McAfee Activation Process.
ReplyDeletemcafee.com/activate
Printer Tech Support is offering best customer service for HP and Lexmark printer users. Best tech support for all printer issue which arises in HP and Lexmark, Experts is available 24/7 at your service.
ReplyDeleteHP Support Number
HP Printer Support Number
HP Helpline Number
HP Technical Support
HP Printer Customer Support Number
Lexmark Customer Support Number
Lexmark Support Number
Lexmark Customer Service
Lexmark Printer Tech Support
Lexmark Printer Support Phone Number
Lexmark Technical Support Number
Lexmark Printer Helpline Number
Adobe users can now find fast and effective solution for their problems related to any of Adobe application on Adobe Contact Number UK. At this number, you can ask anything from our software engineers that are related to Adobe application and we assure you that they will definitely answer your query.
ReplyDelete
ReplyDeleteIf you are having one of such question and looking for an answer then do not worry. We are here to help you. You can call the Norton
Support team and we will provide you with an on-call technician. The technician will take your issue and help you through by providing you
troubleshooting steps.
norton.com/setup
Epson or Seiko Epson Corporation is a Japanese Company which is one of the world’s largest of Printers and imagining related equipment.
With growing demand for a printing device, the technology around printing products is increasing too. This what Epson Printer deliver with
their new and upgraded Printers.pson printer support
epson printer support
Norton Antivirus, Norton Utilities and many others. The company developed a complete tool which can be used as an Antivirus, Anti Malware
as well as internet Security Software. The Norton Antivirus protects the Windows PC, Mac and Mobile Devices from the online threats as
well as the hackers.
norton.com/setup
Brother is another popular Printer company which manufactures advanced printing device and accessories for both personal and business
use. It is a Japanese company which sells their products both online and offline, from stores.
Brother printer support
To setup your echo show device, first download Alexa app on your mobile/ tablet. follow on screen instruction in Alexa app and search for wifi Netwrok and sElect your network enter password and then click on connect button and your Alexa is now connected with wifi.
ReplyDeleteFOR TECHNICAL SUPPORT/ASSISTANCE OF ECHO DOT WIFI SETUP CONTACT: +1-888-409-8111 OR MAIL US: info@activaterokulink.com DESCRIBING YOUR PROBLEM.
setting up Alexa echo show
Echo setup
Echo show setup
HOW TO SETUP ECHO SHOW
DOWNLOAD ALEXA APP
ECHO SHOW
amazon echo alexa helpline number
ReplyDeleteamazon echo alexa customer care number
echo customer service number
echo support number
amazon echo customer service number
echo alexa support
echo customer supportamazon echo tech support
amazon echo customer support number
amazon alexa customer service number
amazon echo technical supportamazon echo customer service
echo tech support
amazon echo customer support
amazon echo alexa tech support number
echo technical support
echo customer service phone number
echo technical support phone number
Amazon echo dot customer service phone number
amazon echo technical support number
Customer service phone number for echo dot
Amazon echo dot customer service number
amazon echo customer care number
echo alexa technical support
echo alexa tech support
echo customer service
amazon echo alexa customer support
amazon echo support number
echo customer support number
echo customer service
amazon echo alexa support number
echo alexa helpline number
amazon echo alexa customer service number
echo customer care phone number
Quicken software give extraordinary performance for the users. Quicken software are famous all over the word. We are third party technical support team and we provide online technical support for those users who are facing some technical error on Quicken software.
ReplyDeleteQuicken technical support number
Quicken tech support number
Quicken customer care number
Quicken customer support phone number
Quicken tech support phone number
Quicken technical support
How HP Printer experts is useful to solve paper jam issues?
ReplyDeleteThe problem related to paper jam will not be a matter of concern for the HP Printer users. it is because of the user dialing HP Printer Support Number UK and then receiving a quality answer. Professionals of HP printer make sure all the correct steps are explained in an understandable manner.
bigpond support
ReplyDeletebigpond support australia
bigpond support number australia
bigpond contact number australia
bigpond phone number australia
bigpond email support australia
bigpond email support
bigpond email support australia
bigpond email support number australia
bigpond email contact number australia
bigpond email phone number australia
If you are a members of Quicken software and facing some technical error on Quicken software, then dial Quicken toll free number and get instant service. We are well known of the Quicken errors, we can resolve any kind of the technical error.
ReplyDeleteQuicken technical support for Creating Bill Reminder
Quicken customer support to Complete Quicken Registration
Quicken technical help for Quicken Bill Pay
Activate Quicken Membership with the help of Quicken technical support number
Quicken customer service number to Recover Quicken Password
Quicken Phone Number to Update Transaction
HP is one of the largest manufacturing electronic devices. It is famous all over the world. HP has releases many devices so far such as HP printer, HP scanner, HP laptop etc.
ReplyDeleteHP technical support number
HP customer support number
HP customer service number
HP customer support phone number
HP technical support phone number
Hey! This post seems to be really helpful for so many people. It feels great to be a support for people out there. We also serve Epson Printer users with instant support for all their issues and queries on our 0808-169-8077 Epson Printer Help Number UK. Call us if you have any problem with your printer.
ReplyDeleteThis is really commendable workaround that has been given in this blog. In case, you are projected to errors as above mentioned, contact the trained officials at Hotmail Customer Support Team UK and resolve all your queries. Hotmail Phone Number UK
ReplyDeleteMicrosoft Office setup is easy to download and install. Activate it now on www.office.com/setup. For any help please call us (800)-368-7751.
ReplyDeleteThank you so much for sharing this valuable information here I am very much sure that this will help many people as there is a huge population that gets stuck with the techniques read more..
ReplyDeleteI was stuck with configuration of my newly purchased printer and was fed up by now, but then this blog posted here proved of much help and my printer is well settled now. One can also get his or her printer issues resolved by talking to the expert sitting at Printer support number uk.Canon Printer Helpline Number UK!
ReplyDeleteNo matter whether you are using Adobe Creative Cloud or any of its application, it is necessary for you to keep the software updated for its smooth functioning. Update also allows you to use all the features of Adobe in correct manner. Dial us at Adobe Helpline Number UK, if you have any issue in updating Adobe.
ReplyDeleteAdobe Help Number UK
Are frequent error prompts from BullGuard Antivirus becoming a cause of concern for you? Has your BullGuard Antivirus yet again stopped updating automatically? Are you facing problems in installing or uninstalling BullGuard Antivirus? Are you still getting adware and malware prompts even after installing BullGuard Antivirus? We offer round the clock BullGuard Support for all such problems. We have a team of highly skilled and experienced BullGuard Technical Support experts who can resolve all such problems quickly. You get high-quality BullGuard Antivirus Help 24 X 7 at the most affordable prices whenever you want. Call us now for help. http://www.bullguard-customer-service.co.uk/
ReplyDeleteAvast is a security providing software its assigned task is to protect the systems from all the infections malware, spyware Trojans and viral attacks. So, it is actually normal if Avast shows up frequent security alerts therefore, if you are getting repeated alerts then it is advisable that you conduct a proper scan on the system. However this will help only if the alerts are getting displayed only on some particular program because then in that case there are high chances of that particular program being infected. If this is not the case then you can simply disable the repeatedly coming up security alerts and continue working. Avast antivirus showing frequent security alerts
ReplyDeletesystem users around the globe are technically sound therefore most of them face many difficulties while performing basic actions of installing and uninstalling of the antivirus. But now such users can take a sigh of relief as the technical support team is here to help them with proper step wise guidance over the same procedures be it installing or uninstalling they will now be able to do it in minutes and up to total accuracy.Technical help in installing or uninstalling the antivirus
ReplyDeleteThis piece written here contains a lot of information, it covers almost everything that is required , but still if something you find missing you can find that by clicking atCanon Printer Phone Number UK
ReplyDeleteThanks for sharing this piece of knowledge here it will help a lot of people in getting their issues fixed also you have written it down in a very impressive manner. keep posting and Get Technical Support for printer visit at HP Printer Help Number UK
ReplyDeleteEpson Printer Contact Number Uk
A very big thanks to whoever has posted this blog here, this blog is really helpful..
ReplyDeleteAVG is an IT software product that keeps the systems safe from all types of malware, spyware Trojans and viral attacks. These types of products do get to face innumerable technical issues and troubles. One stop resolution to all these issues errors and troubles are available at AVG Refund Number UK | AVG Support Number UK
A very big thanks to whoever has posted this blog here, this blog is really helpful..
ReplyDeleteAVG is an IT software product that keeps the systems safe from all types of malware, spyware Trojans and viral attacks. These types of products do get to face innumerable technical issues and troubles. One stop resolution to all these issues errors and troubles are available at AVG Refund Number UK | AVG Support Number UK
You must be aware that now there is no Hotmail and if you want to continue using your Hotmail account then you can do it only through Outlook.com. But if in case you are having any difficulty in getting familiar with new features then call us at Hotmail Toll Free Number UK and allow us to help you.
ReplyDeleteHotmail Helpline Number UK
This blog is a very valuable piece of information
ReplyDeleteAvg Phone Number UK
Avg Support Number UK
McAfee Help Number UK
Such a very useful blog... Thank you for sharing this blog.
ReplyDeleteMcAfee is an antivirus name known in the market from a long period of time. For providing the users with efficient protection measures against all unwanted harmful elements and online threats so that the user can easily keep his or her system protected. For any further guidelines or technical support reach McAfee Helpline Number UK
Thank you for sharing this blog. I am waiting your next blog.
ReplyDeleteAVG is antivirus software that is a bit complicated for the users from non- technical background to understand when it comes to its technical aspects. If in case you are unable to understand and fix any technical issue related to your antivirus on your own then ask support at Avg Support Number UK | Avg Customer Care Number UK
Welcome to Adobe Support Service. For the technical problem, call our Adobe Customer Service Number 1-800-329-1074 for better help
ReplyDeleteAdobe Technical Support
Thanks for this amazing post!!!
ReplyDeleteJuno support phone number
Juno contact number
I was confused badly about how to get my antivirus back to normal working, this piece posted here is really very informative product and thus it helped me a lot.
ReplyDeletekaspersky is an antivirus that keeps the systems safe from all types of malware, spyware Trojans and viral attacks. But this security software often gets into technical issue such as during installation process, uninstalling reinstalling and much more, For proper guidance over all these issues connect at kaspersky Helpline Number UK | kaspersky Help Number UK
http://yahooemailsupportnumber.co.uk/
ReplyDeleteYeah.. Nice post.. Thank you for sharing this post and as are his and your generosity in sharing this explanation and example.
ReplyDeleteMobile Repairing Course in Delhi
Mobile Repairing Institute in Delhi
This is really helpful However,if you come across any technical issue then contact.Brother Phone Number UK
ReplyDeletegarmin support center for your update it.you can change all the information for garmi9n help.
ReplyDeleteWe are here to help you 24/7 for any problem during the roku activation process time.How to enter roku link code and roku com link, www roku com, roku activation and enter roku link code for activation. Call us Toll free: +1-888-381-1555.
ReplyDeleteroku activation
roku com link
The content written here is the best possible way to make a non- technical user to understand the complicated set up of antivirus software. Regular sharing of such content is appreciated.
ReplyDeleteAvast Support Number UK | Avast Refund Number UK | Avast Phone Number UK
ReplyDeleteThis blog is a very valuable piece of information..
Avast Support Number UK | Avast Refund Number UK | Avast Help Number UK
What is your favorite car?
ReplyDeleteLolita
There are few technical problems that can come up with Epson Printers but when you get access to our recovery support you can enjoy the smooth functioning of your printer. We handle all kinds of printer queries whether it is related to your printer driver, any replaceable part or print quality etc, you can contact us at Epson Printer Contact Number UK and find immediate solution for it. Our highly qualified team possesses years of experience which make it easy for them to resolve printer problems in flash of seconds.Epson Printer Support Number UK | Technical Support for Canon Printer | HP Printer Technical Support Number
ReplyDeleteIf it is quite impossible for you to fix the recurring issues, try to deal with them by contacting the technical support team at Hotmail Customer Care Number UK. The technicians know the exact method to be followed for making all the issues disappear. Also, you can reach them 24/7.
ReplyDeleteHotmail Helpline Number UK
We Provide the best technical support for Kaspersky antivirus, Call For Kaspersky Customer, Customer Support For Kaspersky, 24/7 Technical support team available:- kaspersky Support Number | kaspersky Customer UK
ReplyDeleteEpson Printer is simply the best, still at times the user required consideration from the specialist to handle different issues associated with printer machine. Whenever any obstacle comes your way while printing from Epson printer, you should give us a call at Epson Printer Help Desk Number UK. This is the only way to find accurate and permanent solution for your printer query. The administration offered by us is by far the best in the country. Call us now!Epson printer technical support uk
ReplyDeleteThank you for the blog. It's a really very nice your article. Thank you so much for the sharing.
ReplyDeleteVisit:
AOL mail phone number
AOL mail help phone number
AOL mail helpline
AOL mail support
My Gmail wasn’t responding from last few days I was stuck very badly then read this blog and my Gmail id is now working fine. I am very much impressed by the writer’s technical knowledge.
ReplyDeleteGmail Support Number UK | Gmail Help Number UK